And here is what Amazon says about spoofing: http://docs.aws.amazon.com/ses/latest/DeveloperGuide/authentication.html
Because SMTP does not provide any authentication by itself, spammers can send email messages that claim to originate from someone else, while hiding their true origin. By falsifying email headers and spoofing source IP addresses, spammers can mislead recipients into believing that the email messages that they are receiving are authentic.
Most ISPs that forward email traffic take measures to evaluate whether email is legitimate. One such measure that ISPs take is to determine whether an email is authenticated. Authentication requires senders to verify that they are the owner of the account that they are sending from. In some cases, ISPs refuse to forward email that is not authenticated. To ensure optimal deliverability, we recommend that you authenticate your emails.
Authentication mechanisms used by ISPs include:
- Sender Policy Framework (SPF)
- DomainKeys Identified Mail (DKIM)
Also, ensure you comply with Domain-based Message Authentication, Reporting and Conformance (DMARC). DMARC relies on SPF and DKIM
Per the mail in a box instruction guide, check your DKIM and SPF configuration via the DKIM validator. http://dkimvalidator.com/ (Send an email from your spoofed account to the address they provide.)
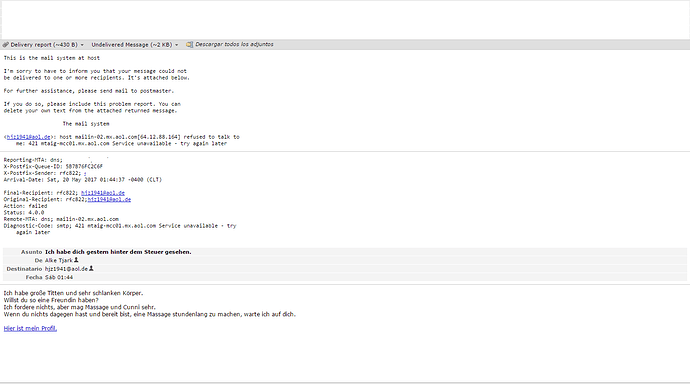
When I ran the dkim validator, it gave me the following error messages:
> Result: permerror (Missing required domain-spec in ‘include:’)
0.0 T_DKIM_INVALID DKIM-Signature header exists but is not valid
I then went to my DNS and created a custom resource record for SPF.
Name = @
Type = SPF
TTL = 1hr
Data = “v=spf1 mx include: box.myserver.com -a -all”
I think it would be great if someone could create detailed, step by step instructions for setting up DMARC, DKIM and SPF records.
More options (per Hover):
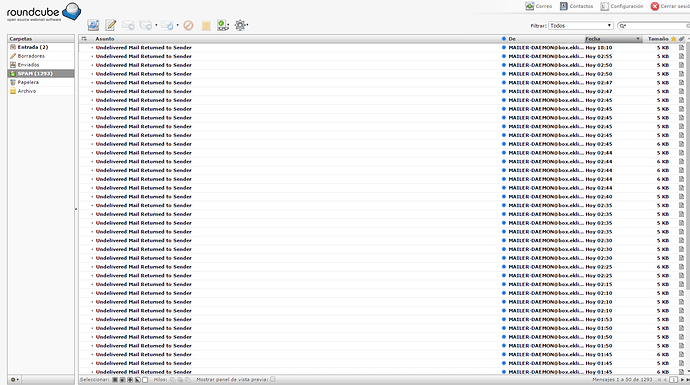
Delete your account
"If the spoofing is recurring and causing a lot of inconvenience, the best thing to do would be to delete the account and start over with a new email account." https://help.hover.com/hc/en-us/articles/217282017-Am-I-being-spoofed-or-has-my-email-been-compromised-
Determine if your account has been compromised
- Look in the email header
- If the header says, “Authenticated sender: sender@senderdomain.com”, your account has been compromised - they have your username and password



- Run a full system virus scan and change your password
Find the spammer
- your bounced emails may contain original source of the email
- find the IP address of where the message originated
- find the ISP
- ask the ISP to put the IP address on a blocklist