Disclaimer:
I’ll be as clear as possible, the following solution will make your MiaB vulnerable to phishing, spam, spoofing attacks and maybe other security risks, as it will let all emails that meet the filter criteria pass through.
I will not take responsibility for any problems that may arise as a result of using the proposed solution.
If you continue, you’ll do it on your own risk.
Now that it’s out of the way, let’s review what we have.
As per the emails attached in your messages:
Postfix rejections are legit as those domains don’t have a valid DNS A or DNS MX records which leads to “Sender address rejected: Domain not found”.
This happens because the filter smtpd_sender_restrictions is set as follow in MiaB:
smtpd_sender_restrictions=
reject_non_fqdn_sender,
reject_unknown_sender_domain,
reject_authenticted_sender_login_mismatch,
reject_rhsbl_sender dbl.spamhaus.org
The way Postfix checks it’s filters is, first hit and your out (email rejected by postfix), as you can see reject_unknown_sender_domain is set as filter number 2, so if the sender hits that filter he’s been rejected.
By the way, the gray list filter isn’t set here, it’s set at smtpd_recipient_restrictions.
So, it doesn’t matter what we put in Postgrey whitelist_clients, because the sender will hit the smtpd_sender_restrictions and not the smtpd_recipient_restrictions.
To bypass the second filter we can add this filter check_sender_access before it.
The check_sender_access checks the “MAIL FROM” header part, so we will create a filter to “Allow” specific domains to pass even if they don’t have a valid DNS A or DNS MX record.
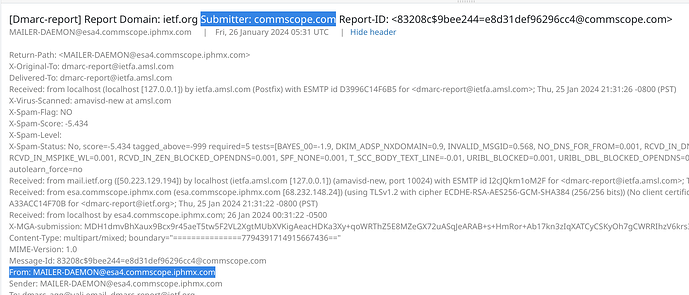
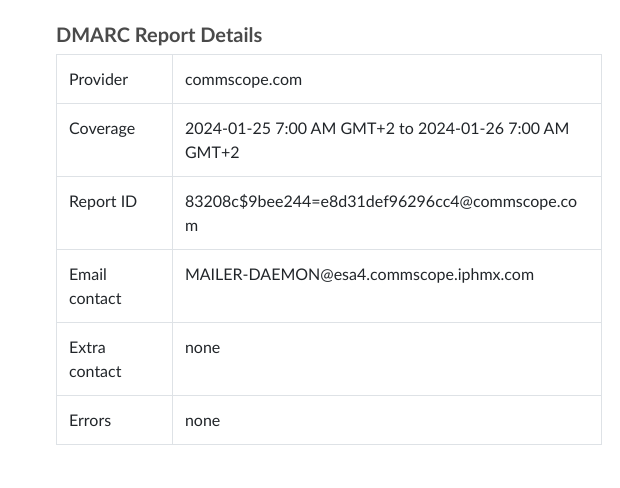
To figure out how this filter should look like, I’ve downloaded a list of the past two years of DMARC reports send to the IETF, only the domains ending with iphmx.com, and came up with a list of 116 entries.
Now that I have some idea of the pattern of those domains, I came up with a filter that will match at least all of the domains in the list with as little room for error (fingers crossed).
Before we’ll create the bypass filter, lets see the reject_unknown_sender_domain in action,
We’ll use telnet on MiaB to do this:
-
Start telnet on localhost:
telnet 127.0.0.1 25
Output:
Trying 127.0.0.1...
Connected to 127.0.0.1.
Escape character is '^]'.
220 box.domain.tld ESMTP
-
Introduce BAD domain using the EHLO command:
ehlo esa4.commscope.iphmx.com
Output:
250-box.domain.tld
250-PIPELINING
250-SIZE 134217728
250-VRFY
250-ETRN
250-STARTTLS
250-ENHANCEDSTATUSCODES
250-8BITMIME
250-DSN
250 CHUNKING
-
Set “mail from” as the BAD email address:
mail from: MAILER-DAEMON@esa4.commscope.iphmx.com
Output:
250 2.1.0 Ok
-
Set the recipient email address to a legitimate email that exists on your server:
rcpt to: admin@box.domain.tld
Output:
450 4.1.8 <MAILER-DAEMON@esa4.commscope.iphmx.com>: Sender address rejected: Domain not found
-
Escape telnet:
Ctrl+]
Output:
^]
telnet>
-
Exit telnet:
quit
Cool, the “error” is there, we can proceed to create the filter.
Remember to backup your settings as they will be overwritten every time there is a new update of MiaB.
How to enable access for unresolved domains:
-
Make a backup of the original main.cf file:
sudo cp /etc/postfix/main.cf /etc/postfix/main.cf.orig
-
Open main.cf with nano
sudo nano /etc/postfix/main.cf
-
Search for the filter: smtpd_sender_restrictions.
Ctrl+w
Enter your search term: smtpd_sender_restrictions
Enter
-
Add check_sender_access regexp:/etc/postfix/cisco_dmarc_sender_access before reject_unknown_sender_domain, don’t forget to put a , at the end of the new line you just added.
Before edit:
smtpd_sender_restrictions=
reject_non_fqdn_sender,
reject_unknown_sender_domain,
reject_authenticated_sender_login_mismatch,
reject_rhsbl_sender dbl.spamhaus.org
After edit:
smtpd_sender_restrictions=
reject_non_fqdn_sender,
check_sender_access regexp:/etc/postfix/cisco_dmarc_sender_access,
reject_unknown_sender_domain,
reject_authenticated_sender_login_mismatch,
reject_rhsbl_sender dbl.spamhaus.org
-
Save changes and exit nano.
Ctrl+x
y
Enter
-
Now we will create the access file: cisco_dmarc_sender_access.
sudo touch /etc/postfix/cisco_dmarc_sender_access
-
Open the file using nano:
sudo nano /etc/postfix/cisco_dmarc_sender_access
-
Paste the following text:
# Cisco Secure Email Threat Defense (DMARC domains)
/esa[0-9]*\.?[acehimnops0-9]*[-]?[0-9]*\.?[acps23]*\.iphmx\.com/i PERMIT
-
Save changes and exit nano.
Ctrl+x
y
Enter
-
Validating the cisco_dmarc_sender_access file.
Valid domain:
sudo postmap -q "MAILER-DAEMON@esa.hc3512-62.iphmx.com" regexp:/etc/postfix/cisco_dmarc_sender_access
Output:
PERMIT
Invalid domain:
sudo postmap -q "MAILER-DAEMON@esa.HC3512-62.iphmx.com" regexp:/etc/postfix/cisco_dmarc_sender_access
Output:
There is no output.
-
Create the database file from cisco_dmarc_sender_access file.
postmap cisco_dmarc_sender_access
-
Apply changes to Postfix.
systemctl restart postfix.service
Finally, we’ll use telnet again, to check if the email will go through this time:
-
Start telnet on localhost:
telnet 127.0.0.1 25
Output:
Trying 127.0.0.1...
Connected to 127.0.0.1.
Escape character is '^]'.
220 box.domain.tld ESMTP
-
Introduce BAD domain using the EHLO command:
ehlo esa4.commscope.iphmx.com
Output:
250-box.domain.tld
250-PIPELINING
250-SIZE 134217728
250-VRFY
250-ETRN
250-STARTTLS
250-ENHANCEDSTATUSCODES
250-8BITMIME
250-DSN
250 CHUNKING
-
Set “mail from” as the BAD email address:
mail from: MAILER-DAEMON@esa4.commscope.iphmx.com
Output:
250 2.1.0 Ok
-
Set the recipient email address to a legitimate email that exists on your server:
rcpt to: admin@box.domain.tld
Output:
250 2.1.5 Ok
-
Run data command:
data
Output:
354 End data with <CR><LF>.<CR><LF>
-
Paste the following text:
subject: DMARC bypass test
Just sent an email from a BAD domain
Thanks,
SysAdmin
.
Output:
250 2.0.0 Ok
-
Terminate the session with the quit command:
quit
Output:
221 2.0.0 Bye
Connection closed by foreign host.
Check the email you entered in step 4 and see if you have received a new mail.
If everything went well, all emails that apply the filter pattern should go through.
How to disable the filter
In case you’ve decided you don’t need the filter anymore and want to remove it, here’s how to do it.
-
Open main.cf with nano
sudo nano /etc/postfix/main.cf
-
Search for the filter: smtpd_sender_restrictions
Ctrl+w
Enter your search term: smtpd_sender_restrictions
Enter
-
Remove check_sender_access regexp:/etc/postfix/cisco_dmarc_sender_access.
Before edit:
smtpd_sender_restrictions=
reject_non_fqdn_sender,
check_sender_access regexp:/etc/postfix/cisco_dmarc_sender_access,
reject_unknown_sender_domain,
reject_authenticated_sender_login_mismatch,
reject_rhsbl_sender dbl.spamhaus.org
After edit:
smtpd_sender_restrictions=
reject_non_fqdn_sender,
reject_unknown_sender_domain,
reject_authenticated_sender_login_mismatch,
reject_rhsbl_sender dbl.spamhaus.org
-
Save changes and exit from nano.
Ctrl+x
y
Enter
-
Delete the files cisco_dmarc_sender_access and cisco_dmarc_sender_access.db.
sudo rm /etc/postfix/cisco_dmarc_sender_access*
-
Applay changes to Postfix.
sudo systemctl restart postfix.service