Hi there,
I installed MIAB back in 2014, not sure which version it was but I can find a file named mailinabox.version with number 5 written in it…
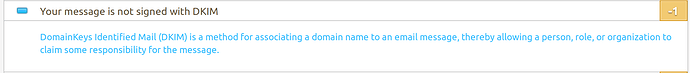
It’s been working well since then, but recently I noticed that DKIM header is not set when sending email (outlook.com is treating my email as spam) and here is the result of https://www.mail-tester.com:
Here is a header of an email sent from my MIAB:
Delivered-To: recipient@receiver.com
Received: by 10.237.37.215 with SMTP id y23csp422107qtc;
Wed, 11 Apr 2018 02:06:14 -0700 (PDT)
X-Google-Smtp-Source: AIpwx4+y4eDDKjGJHA5F0xgbDyuthMUtVF3PYaBTUw9T0RaTYVmOQLk+G7A92ntMs9r1n9iF0z4y
X-Received: by 10.223.150.161 with SMTP id u30mr2663332wrb.151.1523437574330;
Wed, 11 Apr 2018 02:06:14 -0700 (PDT)
ARC-Seal: i=1; a=rsa-sha256; t=1523437574; cv=none;
d=google.com; s=arc-20160816;
b=O+8Thp2tar2wgK9eAiD8RrlwdrCxeqK0N20msHpE3BFQ7W0hExoeGLD6foX5hixWe/
6cB71+ZApkhrEdXuiond8N2p2HPna0dBgmSsrfTQuyEkRlAne2Sj5M164DjwLTkDAJvG
aY/XXoahx12Gx9ifMCt+qbTQUhFWh5cGLLONwDxcx8+cZvWfx9pKyRtLss1QeZFVXH9n
vmH0Ld+hBdLYbZiXV2M0a68WUi5J+vkLxxAFb0HxePllGzlay/nMxj7XScGWjlq8+HZl
yPNOm1OgP4JfbeTGHRLOa4Ra5MYM1AvwzDjSizRuZ91S0pKatTC9qi4cr9Jfo5zihXrc
ZRRw==
ARC-Message-Signature: i=1; a=rsa-sha256; c=relaxed/relaxed; d=google.com; s=arc-20160816;
h=content-language:content-transfer-encoding:mime-version:date
:message-id:subject:from:to:arc-authentication-results;
bh=g3zLYH4xKxcPrHOD18z9YfpQcnk/GaJedfustWU5uGs=;
b=wZGMjh0ZnXfOzf2SUdxnPj6pjMd+R6gEYLDiwl1jV1WKZ3EiZWfNHSrnf8knUsV/c5
1dUvGOHU3gUayR5obXmy8i8ybJZj+u5mvPpl51wKpi8y4hlu3Dj1dA2t46Ofnqq8UczV
4SBuD3ZjmEfXhYHdUvovZ6oYRk6D6rE53H6KNYkuWn4wUrFlE8WPiXHKUOSHk86qgzBG
o3SAZrygK1xxM8oLRvbvYaNZnJyrgwbeN+wIWUqdyFc5rLCtkn5g8Sc2SKREj/D0AC4n
2u1Mx5mxP+xznabXzPlRmN55+/kuA28ZPly0stD9sRMa1RUyQb+DRkK0hQgwNoWclZu6
88/g==
ARC-Authentication-Results: i=1; mx.google.com;
spf=pass (google.com: domain of sender@sender.com designates 94.23.56.200 as permitted sender) smtp.mailfrom=sender@sender.com
Return-Path: <sender@sender.com>
Received: from mail.sender.com (mail.sender.com. [94.23.56.200])
by mx.google.com with ESMTP id v10si541516wrb.104.2018.04.11.02.06.13
for <recipient@receiver.com>;
Wed, 11 Apr 2018 02:06:14 -0700 (PDT)
Received-SPF: pass (google.com: domain of sender@sender.com designates 94.23.56.200 as permitted sender) client-ip=94.23.56.200;
Authentication-Results: mx.google.com;
spf=pass (google.com: domain of sender@sender.com designates 94.23.56.200 as permitted sender) smtp.mailfrom=sender@sender.com
Received: from authenticated-user (unknown [127.0.0.1])
(using TLSv1.2 with cipher ECDHE-RSA-AES128-GCM-SHA256 (128/128 bits))
(No client certificate requested)
by mail.sender.com (Postfix) with ESMTPSA id 613483FF98
for <recipient@receiver.com>; Wed, 11 Apr 2018 11:06:13 +0200 (CEST)
To: Myfirstname MyName <recipient@receiver.com>
From: Myfirstname MyName <sender@sender.com>
Subject: test
Message-ID: <81feab1e-3253-21c7-01ca-ae6c54c1f611@sender.com>
Date: Wed, 11 Apr 2018 11:06:10 +0200
MIME-Version: 1.0
Content-Type: text/plain; charset=utf-8; format=flowed
Content-Transfer-Encoding: 7bit
Content-Language: en-US
Still, I can see I have the folder /mail/dkim with mail.private and mail.txt files, as well as /etc/opendkim.conf:
# This is a basic configuration that can easily be adapted to suit a standard
# installation. For more advanced options, see opendkim.conf(5) and/or
# /usr/share/doc/opendkim/examples/opendkim.conf.sample.
# Log to syslog
Syslog yes
# Required to use local socket with MTAs that access the socket as a non-
# privileged user (e.g. Postfix)
UMask 002
# Sign for example.com with key in /etc/mail/dkim.key using
# selector '2007' (e.g. 2007._domainkey.example.com)
#Domain example.com
#KeyFile /etc/mail/dkim.key
#Selector 2007
# Commonly-used options; the commented-out versions show the defaults.
#Canonicalization simple
#Mode sv
#SubDomains no
#ADSPAction continue
# Always oversign From (sign using actual From and a null From to prevent
# malicious signatures header fields (From and/or others) between the signer
# and the verifier. From is oversigned by default in the Debian pacakge
# because it is often the identity key used by reputation systems and thus
# somewhat security sensitive.
OversignHeaders From
# List domains to use for RFC 6541 DKIM Authorized Third-Party Signatures
# (ATPS) (experimental)
#ATPSDomains example.com
MinimumKeyBits 1024
ExternalIgnoreList refile:/etc/opendkim/TrustedHosts
InternalHosts refile:/etc/opendkim/TrustedHosts
KeyTable refile:/etc/opendkim/KeyTable
SigningTable refile:/etc/opendkim/SigningTable
Socket inet:8891@localhost
RequireSafeKeys false
Anyone could give me a quick diagnostic, and advise on the best way to add DKIM to my mails?
I’m more encline to edit one or two files for a quick and dirty solution than attempting a full update of MIAB (as I believe I probably did some cutomization in the past)
Thank you very much for your advices!
Cheers!