Sorry, my MiaB took a nose dive this morning, with fail2ban using up 100% of 2 of my CPUs on the VM, so I have been rebuilding and restoring most of the day. Hope to have it back up here shortly.
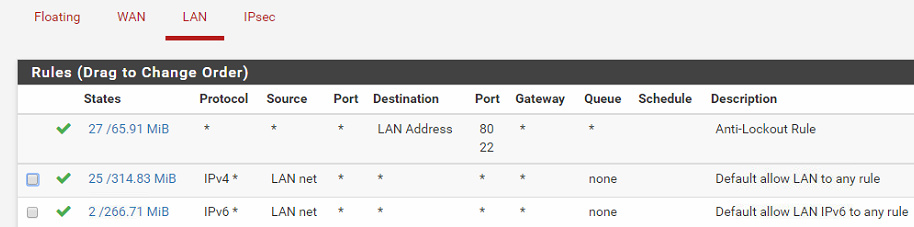
Here is my lan rules.
Remove all of your lan rules related to MiaB. (after taking a backup of your config) as you only use NAT to forward the ports.
Lets get things working 100% first and then I can show you my aliases and how that works.
I am a firm believer in only messing with one thing at a time. If something breaks then it is easier to track down what happened.
Hi Cwilkins,
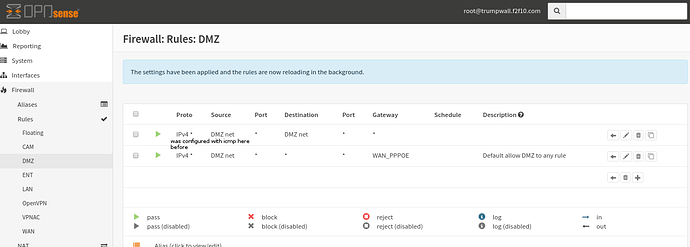
I tried remove my DMZ-DMZ rule and changed my gateway to “default” instead of “WAN_PPPOE”, it works fine.
I, sort of, understand how this works now, but still need to capture some packets to prove.
Because I used VPN client via my VPn provider’s gateway for major traffic for privacy purposes and that VPn client will inject 0.0.0.0/1 and 128.0.0.0/1 to suck all traffic on vpn tunnel. If I didn’t use this “explicit” gateway to “WAN”, it will route this traffic to “default” on router and to VPN tunnel. This is why I used this DMZ-net—DMZ net and with default to WAN GATEWAy for at very beginning.
Now, I am using three vpn client as load-balance and fail-over, I had to block them ‘injecting’ those two routes; so, I can solely rely on “rules” to redirect traffic either to VPN or to WAN. This is why it worked if I set up as yours with not DMZ-net—DMZ net rule and default gateway.
THanks for helping out… I would want try one more time late with OpnSense… The only different setting between pfsense and opnSense is that I used DNS forwarder for pfsense and DNS resolver for opnsense… I am not sure whether that makes diff behaviour…
You had a complex setup, but that is a very interesting way to improve your VPN performance. Are they all the same VPN provider, or are they all different ones? I assume it is the same one, but you are connecting to different end points.
The difference between the DNS resolver and forwarder, is one does the dns look for clients and the other just forwards the request. So it should have no impact but you never know. Let me know if it makes any difference.
You are very welcome. If you can, stick around and give other users help, everyone’s setups are a little different, so we all have different experiences to share.
Yes, I am using vpn.ac provider with 3 locations. You can do same with different providers, just choose option of "blocking routes being injected " on VPn setting, then solely use firewall rules to redirect to a VPN gateway group with all tier 1… If you need some screen capture, I can do that later for you…
doing a bit contribution here. Trying to add something to my old topic which was closed.
Following this guide, you can use /domain/mail, /domain/admin, /domain/cloud, instead of box.domain/cloud,…
-
before upgrade, restore back original files:
backup current working files
mailinabox/conf/nginx-alldomains.conf
mailinabox/conf/nginx-primaryonly.conf
-
modify the above two to achieve the following,
**modify to use f2f10/mail, /cloud, /admin ,instead of box.f2f10.com/cloud & admin
move all configurations from nginx-primaryonly.conf to nginx-alldomains.conf;
and restrict /admin accessed by local subnet only.
location /admin/ {
allow 192.168.0.0/16;
deny all;
-
#modify nextcloud allowed domains…
Owncloud
/usr/local/lib/owncloud/config/config.sample.php
/home/user-data/owncloud/config.php
‘trusted_domains’ =>
array (
0 => ‘f2f10.com’,
1 => ‘voicestream.ca’,
),
important step***
##regenerate /etc/nginx/conf.d/local.conf based on above changed templates…
sudo service postfix reload
sudo service nginx restart
$/home/devnull/mailinabox/tools/web_update
good luck…
@cwilkins
Just reload OpnSense again; I noticed that one of my rules was using ICMP, instead of IPv4. Once it got fixed, Mailinabox checks everything fine. So, it’s not the fault of Pure NAT, it’s my fault of configuration.
That makes me wonder whether you tested it properly when you tried OpnSense. It looks configuration almost exactly with PfSense.
Thanks
peng
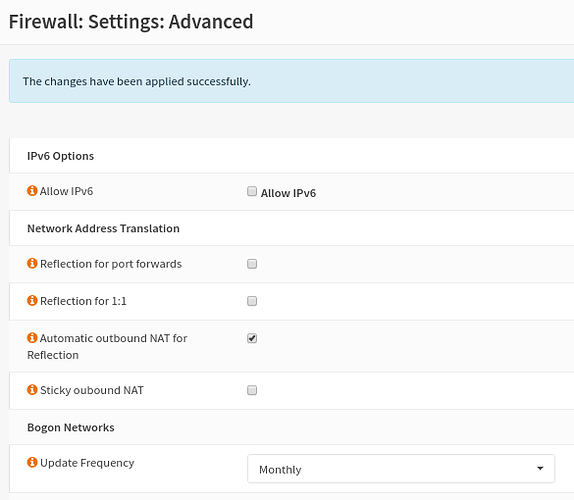
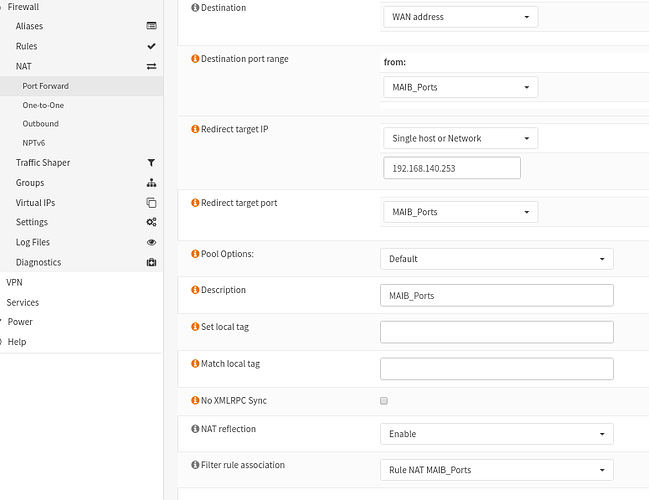
Just tested again, we need setting on Firewall: Settings: Advanced with only Automatic outbound NAT for Reflection being checked.
And, to have NAT Reflection being enabled at Port Forward section.
Also, to make sure traffic is routed to Default Gateway on Firewall, not the WAN IP.
That will make it work.
or , simply choose all setting in Firewall: Settings: Advanced to have them checked, and leave individual nat’s NAT Reflection to default.