I did some screen capture at time of migration so I digged out those and found the date…
I guess the questions is how do we decide whether it’s MAIB or OpnSENSE?
I did some screen capture at time of migration so I digged out those and found the date…
I guess the questions is how do we decide whether it’s MAIB or OpnSENSE?
cwilkins
I will look into that, OpnSense is almost identical to PfSense…Just dont know where I can find that setting yet…
tcpdump -ni lo port 53
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on lo, link-type EN10MB (Ethernet), capture size 262144 bytes
18:18:02.470672 IP 127.0.0.1.52154 > 127.0.0.1.53: 5124+ A? www.voicestream.ca. (36)
18:18:04.572849 IP 127.0.0.1.54443 > 127.0.0.1.53: 5124+ A? www.voicestream.ca. (36)
18:18:06.775096 IP 127.0.0.1.33089 > 127.0.0.1.53: 5124+ A? www.voicestream.ca. (36)
18:18:09.177491 IP 127.0.0.1.57552 > 127.0.0.1.53: 5124+ A? www.voicestream.ca. (36)
18:18:11.980666 IP 127.0.0.1.54333 > 127.0.0.1.53: 5124+ A? www.voicestream.ca. (36)
18:18:12.471278 IP 127.0.0.1.53 > 127.0.0.1.54443: 5124 ServFail 0/0/0 (36)
18:18:12.471278 IP 127.0.0.1.53 > 127.0.0.1.52154: 5124 ServFail 0/0/0 (36)
18:18:12.471281 IP 127.0.0.1.53 > 127.0.0.1.57552: 5124 ServFail 0/0/0 (36)
18:18:12.471415 IP 127.0.0.1.53 > 127.0.0.1.54333: 5124 ServFail 0/0/0 (36)
18:18:12.473293 IP 127.0.0.1.60165 > 127.0.0.1.53: 48234+ A? box.f2f10.com. (31)
18:18:14.575449 IP 127.0.0.1.52992 > 127.0.0.1.53: 48234+ A? box.f2f10.com. (31)
18:18:16.777720 IP 127.0.0.1.34182 > 127.0.0.1.53: 48234+ A? box.f2f10.com. (31)
18:18:19.180127 IP 127.0.0.1.51617 > 127.0.0.1.53: 48234+ A? box.f2f10.com. (31)
18:18:21.982947 IP 127.0.0.1.58452 > 127.0.0.1.53: 48234+ A? box.f2f10.com. (31)
18:18:22.473974 IP 127.0.0.1.53 > 127.0.0.1.34182: 48234 ServFail 0/0/0 (31)
18:18:22.473976 IP 127.0.0.1.53 > 127.0.0.1.60165: 48234 ServFail 0/0/0 (31)
18:18:22.473976 IP 127.0.0.1.53 > 127.0.0.1.52992: 48234 ServFail 0/0/0 (31)
18:18:22.474131 IP 127.0.0.1.53 > 127.0.0.1.51617: 48234 ServFail 0/0/0 (31)
18:18:22.474134 IP 127.0.0.1.53 > 127.0.0.1.58452: 48234 ServFail 0/0/0 (31)
18:18:22.476046 IP 127.0.0.1.44917 > 127.0.0.1.53: 6087+ A? f2f10.com. (27)
18:18:24.578109 IP 127.0.0.1.35246 > 127.0.0.1.53: 6087+ A? f2f10.com. (27)
18:18:26.780322 IP 127.0.0.1.53307 > 127.0.0.1.53: 6087+ A? f2f10.com. (27)
18:18:29.182771 IP 127.0.0.1.51832 > 127.0.0.1.53: 6087+ A? f2f10.com. (27)
18:18:31.985562 IP 127.0.0.1.44269 > 127.0.0.1.53: 6087+ A? f2f10.com. (27)
18:18:32.476747 IP 127.0.0.1.53 > 127.0.0.1.44917: 6087 ServFail 0/0/0 (27)
18:18:32.476746 IP 127.0.0.1.53 > 127.0.0.1.35246: 6087 ServFail 0/0/0 (27)
18:18:32.476773 IP 127.0.0.1.53 > 127.0.0.1.53307: 6087 ServFail 0/0/0 (27)
18:18:32.476865 IP 127.0.0.1.53 > 127.0.0.1.51832: 6087 ServFail 0/0/0 (27)
18:18:32.478782 IP 127.0.0.1.47415 > 127.0.0.1.53: 43178+ A? www.f2f10.com. (31)
18:18:34.580915 IP 127.0.0.1.51004 > 127.0.0.1.53: 43178+ A? www.f2f10.com. (31)
18:18:36.783210 IP 127.0.0.1.49761 > 127.0.0.1.53: 43178+ A? www.f2f10.com. (31)
18:18:39.185641 IP 127.0.0.1.45442 > 127.0.0.1.53: 43178+ A? www.f2f10.com. (31)
18:18:41.988394 IP 127.0.0.1.35898 > 127.0.0.1.53: 43178+ A? www.f2f10.com. (31)
18:18:42.479552 IP 127.0.0.1.53 > 127.0.0.1.51004: 43178 ServFail 0/0/0 (31)
18:18:42.479554 IP 127.0.0.1.53 > 127.0.0.1.49761: 43178 ServFail 0/0/0 (31)
18:18:42.479554 IP 127.0.0.1.53 > 127.0.0.1.47415: 43178 ServFail 0/0/0 (31)
18:18:42.479667 IP 127.0.0.1.53 > 127.0.0.1.35898: 43178 ServFail 0/0/0 (31)
18:18:42.479673 IP 127.0.0.1.53 > 127.0.0.1.45442: 43178 ServFail 0/0/0 (31)
18:18:42.481540 IP 127.0.0.1.34940 > 127.0.0.1.53: 58537+ A? voicestream.ca. (32)
looks like an internal MAiB dns service issue to me…
this is output when I do "
udo /home/devnull/mailinabox/management/ssl_certificates.py
No TLS certificates could be provisoned at this time:
box.f2f10.com: DNS isn’t configured properly for this domain: DNS resolution failed (A: All nameservers failed to answer the query box.f2f10.com. IN A: Server 127.0.0.1 UDP port 53 answered The DNS operation timed out.; Server 127.0.0.1 UDP port 53 answered The DNS operation timed out.; Server 127.0.0.1 UDP port 53 answered The DNS operation timed out.; Server 127.0.0.1 UDP port 53 answered The DNS operation timed out.; Server 127.0.0.1 UDP port 53 answered SERVFAIL).
could that MAIB get some configuration files lost? I tried to WEB in admin page, the status section says “something wrong” and TLS Cert section says “something wrong”; other sections are ok.
really confused…
but, it works for normal email client program to leverage DNS in MAIB…how come?
this is when I am using email client (KDE Mail or Claws)… I can see on the tcpdump output…
18:22:28.735009 IP 127.0.0.1.49561 > 127.0.0.1.53: 17707+ PTR? 153.110.168.192.in-addr.arpa. (46)
18:22:28.735415 IP 127.0.0.1.53 > 127.0.0.1.49561: 17707 NXDomain* 0/1/0 (101)
18:22:28.892526 IP 127.0.0.1.39058 > 127.0.0.1.53: 3334+ A? f2f10.com.dbl.spamhaus.org. (44)
18:22:28.907074 IP 127.0.0.1.53 > 127.0.0.1.39058: 3334 NXDomain 0/1/0 (108)
18:22:29.020445 IP 127.0.0.1.52701 > 127.0.0.1.53: 16441+ [1au] MX? dh.com. (35)
18:22:29.347960 IP 127.0.0.1.53 > 127.0.0.1.52701: 16441 2/6/3 MX mx1.dhltd.iphmx.com. 10, MX mx2.dhltd.iphmx.com. 10 (250)
18:22:29.348097 IP 127.0.0.1.51641 > 127.0.0.1.53: 25344+ A? mx1.dhltd.iphmx.com. (37)
18:22:29.502234 IP 127.0.0.1.53 > 127.0.0.1.51641: 25344 3/8/0 A 68.232.131.30, A 68.232.140.103, A 68.232.143.79 (260)
18:22:29.502382 IP 127.0.0.1.34481 > 127.0.0.1.53: 32132+ AAAA? mx1.dhltd.iphmx.com. (37)
18:22:29.509720 IP 127.0.0.1.53 > 127.0.0.1.34481: 32132 0/1/0 (110)
18:22:29.509855 IP 127.0.0.1.55997 > 127.0.0.1.53: 56454+ A? mx2.dhltd.iphmx.com. (37)
18:22:29.517230 IP 127.0.0.1.53 > 127.0.0.1.55997: 56454 3/8/0 A 68.232.143.79, A 68.232.140.103, A 68.232.131.30 (260)
18:22:29.517418 IP 127.0.0.1.40399 > 127.0.0.1.53: 28477+ AAAA? mx2.dhltd.iphmx.com. (37)
18:22:29.537362 IP 127.0.0.1.53 > 127.0.0.1.40399: 28477 0/1/0 (110)
18:22:41.821469 IP 127.0.0.1.49391 > 127.0.0.1.53: 21109+ PTR? 103.140.232.68.in-addr.arpa. (45)
18:22:42.090267 IP 127.0.0.1.53 > 127.0.0.1.49391: 21109 2/8/0 CNAME 103.140.232.68.in-addr.arpa.iphmx.com., PTR esa2.dhltd.iphmx.com. (296)
18:22:42.090527 IP 127.0.0.1.57595 > 127.0.0.1.53: 63812+ A? esa2.dhltd.iphmx.com. (38)
18:22:42.097376 IP 127.0.0.1.53 > 127.0.0.1.57595: 63812 1/8/0 A 68.232.140.103 (229)
18:22:42.618645 IP 127.0.0.1.38667 > 127.0.0.1.53: 50651+ A? 103.140.232.68.zen.spamhaus.org. (49)
18:22:42.722595 IP 127.0.0.1.53 > 127.0.0.1.38667: 50651 NXDomain 0/1/0 (113)
18:22:42.724562 IP 127.0.0.1.57630 > 127.0.0.1.53: 56728+ A? 103.140.232.68.list.dnswl.org. (47)
18:22:42.881400 IP 127.0.0.1.53 > 127.0.0.1.57630: 56728 1/5/12 A 127.0.3.1 (410)
18:22:43.303878 IP 127.0.0.1.60282 > 127.0.0.1.53: 2128+ [1au] TXT? _dmarc.cisco.com. (45)
18:22:43.426783 IP 127.0.0.1.53 > 127.0.0.1.60282: 2128 1/3/7 TXT "v=DMARC1; p=none; fo=1; ri=3600; rua=
tried cisco.com users as well…
18:24:58.662242 IP 192.168.140.253.4715 > 85.94.194.12.53: 36431% [1au] A? f2f10.com.dbl.spamhaus.org. (55)
18:24:58.768412 IP 85.94.194.12.53 > 192.168.140.253.4715: 36431 NXDomain*- 0/1/0 (108)
18:24:58.768926 IP 192.168.140.253.12562 > 192.112.36.4.53: 55446% [1au] DS? spamhaus.org. (41)
18:24:58.768926 IP 192.168.140.253.1792 > 192.112.36.4.53: 1125% [1au] NS? . (28)
18:24:58.820385 IP 192.112.36.4.53 > 192.168.140.253.12562: 55446- 0/9/13 (814)
18:24:58.820693 IP 192.168.140.253.36538 > 199.249.112.1.53: 27861% [1au] DS? spamhaus.org. (41)
18:24:58.826904 IP 192.112.36.4.53 > 192.168.140.253.1792: 1125*- 14/0/27 NS b.root-servers.net., NS h.root-servers.net., NS e.root-servers.net., NS j.root-servers.net., NS m.root-servers.net., NS l.root-servers.net., NS g.root-servers.net., NS k.root-servers.net., NS d.root-servers.net., NS f.root-servers.net., NS a.root-servers.net., NS i.root-servers.net., NS c.root-servers.net., RRSIG (1097)
18:24:58.827574 IP 199.249.112.1.53 > 192.168.140.253.36538: 27861*- 0/6/1 (760)
18:24:58.827836 IP 192.168.140.253.36594 > 199.249.112.1.53: 6669% [1au] DNSKEY? org. (32)
18:24:58.835398 IP 199.249.112.1.53 > 192.168.140.253.36594: 6669*- 7/0/1 DNSKEY, DNSKEY, DNSKEY, DNSKEY, RRSIG, RRSIG, RRSIG[|domain]
18:24:58.954425 IP 192.168.140.253.47362 > 64.102.255.44.53: 42860% [1au] A? alln-mx-01.cisco.com. (49)
18:24:58.982422 IP 64.102.255.44.53 > 192.168.140.253.47362: 42860*- 1/3/7 A 173.37.147.230 (251)
18:24:58.983052 IP 192.168.140.253.18767 > 72.163.5.201.53: 30383% [1au] AAAA? alln-mx-01.cisco.com. (49)
18:24:59.029650 IP 72.163.5.201.53 > 192.168.140.253.18767: 30383*- 1/3/7 AAAA 2001:420:1201:6::ad25:93e6 (263)
18:24:59.030355 IP 192.168.140.253.19362 > 64.102.255.44.53: 48817% [1au] A? rcdn-mx-01.cisco.com. (49)
18:24:59.058058 IP 64.102.255.44.53 > 192.168.140.253.19362: 48817*- 1/3/7 A 72.163.7.166 (251)
18:24:59.058664 IP 192.168.140.253.32711 > 173.37.146.41.53: 54407% [1au] AAAA? rcdn-mx-01.cisco.com. (49)
18:24:59.099600 IP 173.37.146.41.53 > 192.168.140.253.32711: 54407*- 0/1/1 (100)
18:24:59.100202 IP 192.168.140.253.20340 > 64.102.255.44.53: 25637% [1au] A? aer-mx-01.cisco.com. (48)
18:24:59.128083 IP 64.102.255.44.53 > 192.168.140.253.20340: 25637*- 1/3/7 A 173.38.212.150 (250)
18:24:59.128785 IP 192.168.140.253.49298 > 64.102.255.44.53: 32695% [1au] AAAA? aer-mx-01.cisco.com. (48)
18:24:59.156589 IP 64.102.255.44.53 > 192.168.140.253.49298: 32695*- 1/3/7 AAAA 2001:420:4621::ad26:d496 (262)
18:24:59.281018 IP 204.194.238.161.2037 > 192.168.140.253.53: 62180 [1au] A? box.f2f10.com. (42)
18:24:59.281088 IP 192.168.140.253.53 > 204.194.238.161.2037: 62180*- 1/2/3 A 76.10.176.225 (126)
18:24:59.929279 IP 204.194.238.164.47535 > 192.168.140.253.53: 964 [1au] MX? f2f10.com. (38)
18:24:59.929416 IP 192.168.140.253.53 > 204.194.238.164.47535: 964*- 1/2/4 MX box.f2f10.com. 10 (142)
18:24:59.973505 IP 204.194.238.170.36734 > 192.168.140.253.53: 35203 [1au] AAAA? box.f2f10.com. (42)
18:24:59.973628 IP 192.168.140.253.53 > 204.194.238.170.36734: 35203*- 0/1/1 (93)
18:25:00.114708 IP 204.194.238.164.10791 > 192.168.140.253.53: 22691 [1au] TXT? box.f2f10.com. (42)
18:25:00.114814 IP 192.168.140.253.53 > 204.194.238.164.10791: 22691*- 1/2/3 TXT “v=spf1 mx -all” (137)
18:25:00.159019 IP 204.194.238.168.3571 > 192.168.140.253.53: 2305 [1au] MX? box.f2f10.com. (42)
18:25:00.159151 IP 192.168.140.253.53 > 204.194.238.168.3571: 2305*- 1/2/4 MX box.f2f10.com. 10 (142)
18:25:00.202476 IP 204.194.238.161.6411 > 192.168.140.253.53: 54734 [1au] TXT? f2f10.com. (38)
18:25:00.202566 IP 192.168.140.253.53 > 204.194.238.161.6411: 54734*- 1/2/3 TXT “v=spf1 mx -all” (137)
18:25:00.320783 IP 204.194.238.163.45143 > 192.168.140.253.53: 59573 [1au] TXT? mail._domainkey.f2f10.com. (54)
18:25:00.320887 IP 192.168.140.253.53 > 204.194.238.163.45143: 59573*- 1/2/3 TXT “v=DKIM1; k=rsa; s=email; p=MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAwNcfRLgpvsYPKA3toCoi08jsPDE/OSb6GrtnDWUEzUuOgDlMOROXRbYMbjZydd0bsYQbpMI32+nQwPFRYI9f8HgkuEDA0tYxrDftJXLy9/AEQMJxJED6aMXqcmlW0KAAtOO1yDE8ICDcoK3mLLb13dky/y88dE3e4P6/bKmKVuwG0OlmD9AINBkU” “OWZ+uGH1bmfvst0hTLdVbogICBHqMa2HmKfdhjojHGO/hYS2pqB8OlP9BknAC6n4lFV8ud/tmPXsDTRhNF5SE5/vg4CQdVqZfUGCXwk+ucU/kmJ5fjcQrp9zshcYEeJU24tFQWj/XweanvXZQfaTXnTsD1ELHwIDAQAB” (559)
18:25:00.374767 IP 204.194.238.168.13673 > 192.168.140.253.53: 44590 [1au] TXT? _dmarc.f2f10.com. (45)
18:25:00.374869 IP 192.168.140.253.53 > 204.194.238.168.13673: 44590*- 1/2/3 TXT “v=DMARC1; p=quarantine” (152)
18:25:00.514771 IP 204.194.238.168.18323 > 192.168.140.253.53: 24627 [1au] A? f2f10.com. (38)
18:25:00.514867 IP 192.168.140.253.53 > 204.194.238.168.18323: 24627*- 1/2/3 A 76.10.176.225 (126)
18:25:00.522429 IP 204.194.238.170.10267 > 192.168.140.253.53: 15475 [1au] A? www.f2f10.com. (42)
18:25:00.522631 IP 192.168.140.253.53 > 204.194.238.170.10267: 15475*- 1/2/3 A 76.10.176.225 (130)
18:25:01.930513 IP 204.194.238.167.33073 > 192.168.140.253.53: 1446 [1au] MX? f2f10.com. (38)
18:25:01.930617 IP 192.168.140.253.53 > 204.194.238.167.33073: 1446*- 1/2/4 MX box.f2f10.com. 10 (142)
18:25:01.986483 IP 204.194.238.169.51886 > 192.168.140.253.53: 20211 [1au] A? box.f2f10.com. (42)
18:25:01.986578 IP 192.168.140.253.53 > 204.194.238.169.51886: 20211*- 1/2/3 A 76.10.176.225 (126)
18:25:02.079504 IP 192.168.140.253.42826 > 199.180.182.53.53: 25500% [1au] PTR? 79.86.37.173.in-addr.arpa. (54)
18:25:02.136394 IP 199.180.182.53.53 > 192.168.140.253.42826: 25500- 0/8/1 (382)
18:25:02.136757 IP 192.168.140.253.44047 > 204.61.216.50.53: 5003% [1au] PTR? 79.86.37.173.in-addr.arpa. (54)
18:25:02.143833 IP 204.61.216.50.53 > 192.168.140.253.44047: 5003- 0/4/1 (316)
18:25:02.144225 IP 192.168.140.253.54950 > 72.163.5.201.53: 48474% [1au] PTR? 79.86.37.173.in-addr.arpa. (54)
18:25:02.190495 IP 72.163.5.201.53 > 192.168.140.253.54950: 48474*- 1/3/7 PTR rcdn-iport-8.cisco.com. (276)
18:25:02.191182 IP 192.168.140.253.18356 > 192.203.230.10.53: 2973% [1au] DS? 173.in-addr.arpa. (45)
18:25:02.191301 IP 192.168.140.253.56217 > 192.203.230.10.53: 27963% [1au] NS? . (28)
18:25:02.198088 IP 192.203.230.10.53 > 192.168.140.253.18356: 2973- 0/10/13 (729)
18:25:02.198570 IP 192.203.230.10.53 > 192.168.140.253.56217: 27963*- 14/0/27 NS a.root-servers.net., NS b.root-servers.net., NS c.root-servers.net., NS d.root-servers.net., NS e.root-servers.net., NS f.root-servers.net., NS g.root-servers.net., NS h.root-servers.net., NS i.root-servers.net., NS j.root-servers.net., NS k.root-servers.net., NS l.root-servers.net., NS m.root-servers.net., RRSIG (1097)
18:25:02.198620 IP 192.168.140.253.61343 > 199.180.182.53.53: 20316% [1au] DS? 173.in-addr.arpa. (45)
18:25:02.256341 IP 199.180.182.53.53 > 192.168.140.253.61343: 20316*- 2/0/1 DS, RRSIG (253)
18:25:02.256865 IP 192.168.140.253.59415 > 199.180.182.53.53: 55009% [1au] DS? 37.173.in-addr.arpa. (48)
18:25:02.327153 IP 199.180.182.53.53 > 192.168.140.253.59415: 55009- 0/8/1 (376)
18:25:02.327482 IP 192.168.140.253.56919 > 204.61.216.50.53: 21174% [1au] DS? 37.173.in-addr.arpa. (48)
18:25:02.334601 IP 204.61.216.50.53 > 192.168.140.2
really muddy for the moment…
these examples must prove that DNS is working then…but what’s going wrong with those CERT and DNS error thing that failed my CERT renew???/ Puzzled…
n the future it is expected that many, if not all, open source distributions will move to Unbound and away from BIND. FreeBSD 10 has already made the change as BIND is no longer included in the default install. BIND, also known as named, is getting extremely code bloated, slow and over complicated. Complication leads to security exploits and over twenty(20) of the last seventy(70) critical bugs in FreeBSD have been due to BIND itself. The other problem is BIND is used for around 70% of the worlds DNS servers leading to a monoculture environment. When an attack or exploit comes out it is advantageous as the attacker to go after the most used software. Unbound in comparison is an incredibly fast and secure DNS name server which, due to its small size, can easily be code audited for security.
So, “named” on the box is “bind”…then, what is that “nsd4” stuff in the status check then?
tcp 0 0 127.0.0.1:53 0.0.0.0:* LISTEN 4494/named
tcp 0 0 127.0.0.1:953 0.0.0.0:* LISTEN 4494/named
udp 0 0 127.0.0.1:53 0.0.0.0:* 4494/named

 Public DNS (nsd4) is not running (port 53).
Public DNS (nsd4) is not running (port 53).
I have /etc/bind/xxxx and /etc/nsd/xxx in MAIB…however, my ns1.box.xxxx and ns2.box.xxx info is under /etc/nsd/xxx zone files, not in /etc/bind/xxx zone files.
Could this be a problem? That NSD is not running but Bind is runing can can not locate that ns1 and ns2?
I have these info configured via WEB ADmin portal… If this is not correct, then why is under /etc/nsd…?
do you guys have similar info in /etc/bind and /etc/nsd/ ? Under which directory is your zone info ?
~# pstree
init-±acpid
|-atd
|-cron
|-dbus-daemon
|-dovecot-±anvil
| |-2*[auth]
| |-config
| |-imap
| |-imap-login
| |-log
| -ssl-params |-fail2ban-server---20*[{fail2ban-server}] |-irqbalance |-mailinabox-daem |-master-+-anvil | |-pickup | |-qmgr | |-smtpd |-tlsmgr
|-memcached—5*[{memcached}]
|-munin-node
|-named—6[{named}]*
|-nginx—4*[nginx]
|-nsd—nsd—nsd
|-ntpd
|-opendkim—6*[{opendkim}]
|-opendmarc—5*[{opendmarc}]
|-php-fpm7.0—php-fpm7.0
|-php5-fpm—2*[php5-fpm]
|-postgrey --pidf
|-rsyslogd—2*[{rsyslogd}]
|-spampd—3*[spampd]
|-sshd—2*[sshd—sshd—bash]
|-systemd-logind
|-systemd-udevd
|-upstart-file-br
|-upstart-socket-
`-upstart-udev-brstrong text
The following files indicates that MAIB is doing something on this “nsd4” thing…
cat /etc/nsd/nsd.conf
server:
hide-version: yes
identity: “”
zonesdir: “/etc/nsd/zones”
ip-transparent: yes
ip-address: 192.168.140.253
include: /etc/nsd/zones.conf
Should it be “nsd4” running on UDP53 , instead of “bind” or “named” on UDP 53?
https://mxtoolbox.com/SuperTool.aspx?action=mx%3Af2f10.com&run=toolpage#
This seems to show that my ns1.box.f2f10.com and ns2.box.f2f10.com works as well…
So, what’s all this about Let’s encrypt cert and dns errors’s root cause then???
Any thoughts are appreciated!
I was wondering whether you may have some time offering a hand on this …thanks in advance!
bind 4494 0.0 0.3 416068 51300 ? Ssl 16:03 0:04 /usr/sbin/named -u bind -4
nsd 4954 0.0 0.1 51820 28304 ? Ss 16:03 0:00 /usr/sbin/nsd -d -c /etc/nsd/nsd.conf
nsd 4957 0.0 0.2 58412 34328 ? S 16:03 0:00 /usr/sbin/nsd -d -c /etc/nsd/nsd.conf
nsd 4958 0.0 0.0 58804 9760 ? S 16:03 0:00 /usr/sbin/nsd -d -c /etc/nsd/nsd.conf
Hello miabatf2f10,
Sorry I was traveling yesterday for the rest of the day after my last response.
I still think this is a NAT Reflection issue with opnSense. Did you find the spot to change that in openSense yet? I just tested in my environment and once I turn back off that setting in pfSense I get DNS not running on port 53.
The MiaB has to be able to resolve it’s domain name to an public IP, however when most firewalls respond to internal DNS requests it will reply with the private IP address, not the public one.
What IP do you get when you try to ping box.YOURDOMAIN.com from the same vlan?
Here is a sample of what I get with NAT Reflection turned off in pfSense for my MiaB.
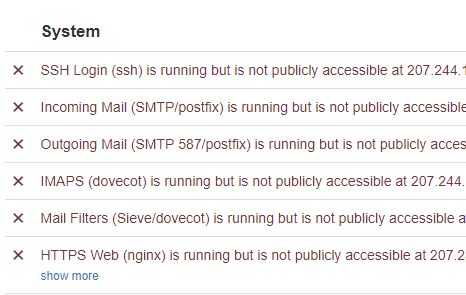
When I reenable it the errors go away.
Any way we can remove the opnSense from the troubleshooting, and put this box right on the internet without that in the way?
Thanks!
Chess